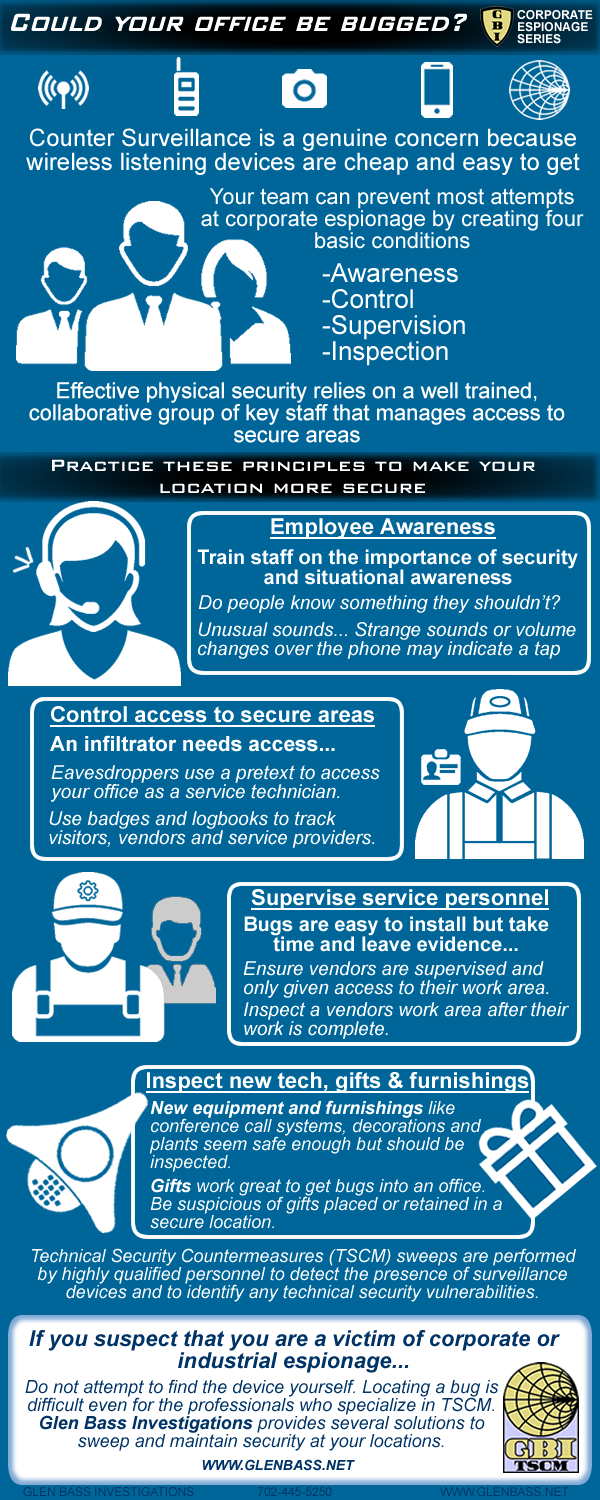
Prevent Corporate Espionage and Eavesdropping by employing 2022 Enhanced Protocol
Is your organization vulnerable to eavesdropping or video surveillance?
How easy is it to eavesdrop on your organizations confidential information?
Training your staff in four simple processes will help protect your business, your confidential information and your employees.
Prevent Eavesdropping and Protect Privacy in 4 easy steps
Protection against the installation of eavesdropping devices or "Bugs" in 2022 enhanced protocol requires
- Awareness: Train staff on the importance of security and situational awareness
- Control: Control access to secure areas with visitor badges and logbooks
- Supervision: Bugs take time to install, supervise service personnel
- Inspection: Inspect new technology, gifts and furnishings
Train 2022 Security Protocol
When a business does not strive tp prevent eavesdropping, corporate espionage is easy. Placing a listening device or hidden camera in a location requires access and just a moment of time. Maintaining a businesses competitive edge is critical to achieving its corporate goals.
For many organizations, its most valuable asset is its intellectual property, proprietary processes, marketing strategies and otherwise confidential information.
Practicing these enhanced protocols will protect your business from eavesdropping and surveillance attempts.
Corporate Espionage Series (CES)
CES provides easy steps to better protect your organizations privacy
Glen Bass Investigations provides Corporate Bug Sweep Services
GBI offers a wide range of counter espionage and TSCM services. GBI can help you minimize your losses and improve your companies bottom line by reviewing it's internal security and ensuring your employees understand Technical Surveillance Countermeasures (T.S.C.M.).
A Technical Security Countermeasures or TSCM Sweep is a service provided by highly qualified personnel to detect the presence of surveillance devices and to identify technical security vulnerabilities of the site in question.
GBI uses proven techniques & decades experience in Counter-Surveillance & Technical Security Counter Measures (Bug Sweeps) to secure our clients locations
Share on Facebook Share on LinkedIn
Share this Image On Your Site
What is a Corporate Bug Sweep
Technology is constantly evolving. The technical aspects of Eavesdropping, (audio, video, cell phones, computer spy ware and GPS devices), has grown and these devices and methodologies are becoming easier, cheaper and better.
Only you know if you have reason to believe whether someone is listening or watching, and if you think they are, then they probably are. Technical Surveillance Countermeasures or TSCM, is also known by the reference of a Bug Sweep, TSCM Bug Sweep, and the more modern name of Electronic Eavesdropping Detection or EED. We are Certified Specialists in the detection and location of eavesdropping devices.
In Minnesota as in most states, you need to be a licensed Private Investigator to conduct a corporate bug sweep. We are licensed to do so, which allows us to do compete consulting work while protecting your interests. We operate the latest REI counter-eavesdropping equipment and can ensure complete confidentiality.